PFP can use data collected from un-intended EMI signals on power line to a device, ground loop, current, RF, acoustic, etc.
PFP senses the EMI coming off of a chip, board or device through a probe connected to the pMon device.
pMon is a power monitor device, PFP supports many commercial on the shelf devices such as software defined radio (NUAND BladeRF, Nooelec NESDR, Ettus, etc.), test instruments, embedded devices such as Raspberry Pi, etc. The pMon-751 allows the user to monitor a wide variety of target devices, from chips, to boards, and to systems, directly EMI, or via DC using an inductive current probe.
PFP supports commonly used instruments such as the Keysight 3324 Current Analyzer, National Instruments, HP, Tektronix, and other interfaces. Embedded designers could use the analog-to-digital converter (ADC) on a chip or in the device to collect data from side-channel signals.
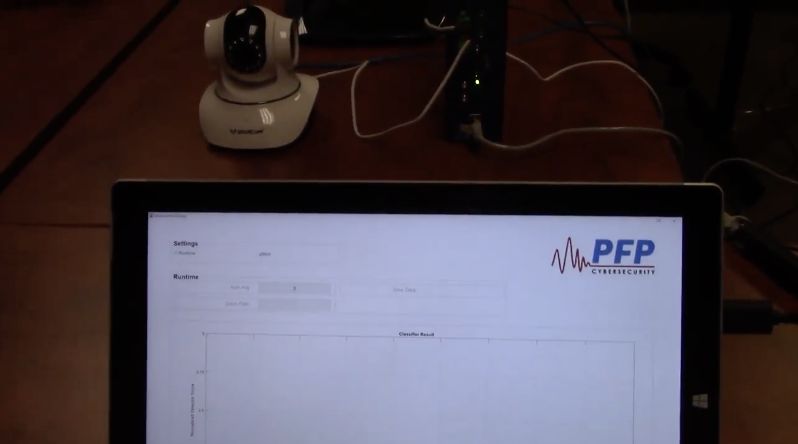
P3Scan is PFP’s open platform software that lives in the cloud (on AWS) or on-premise. The product is web-enabled and dashboard accessible from any location. Users can log-on and monitor their data through the web.
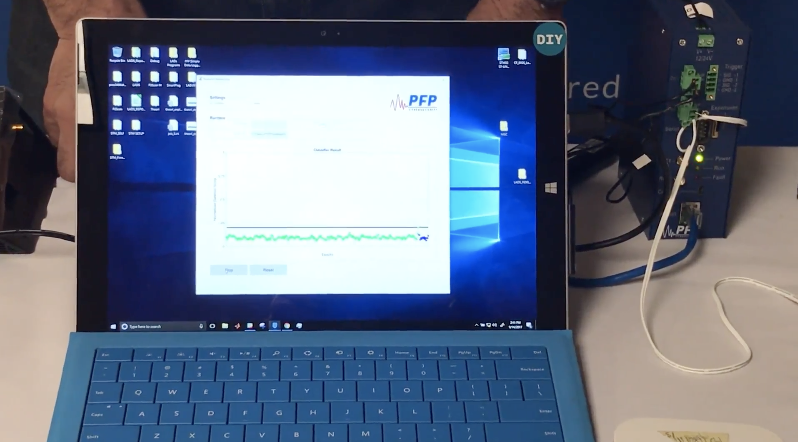
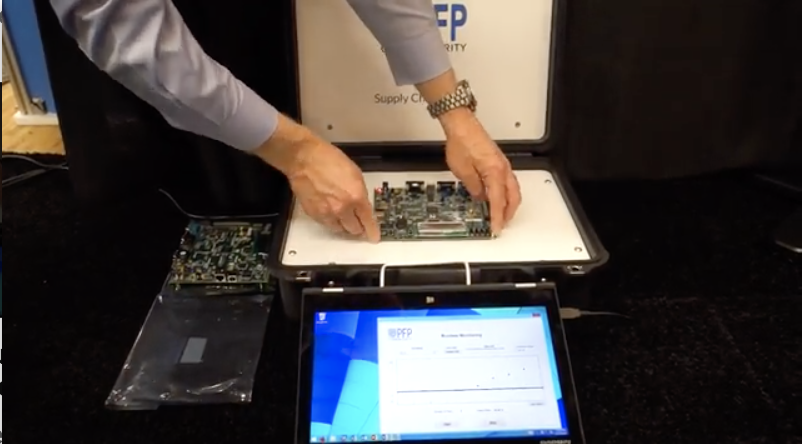
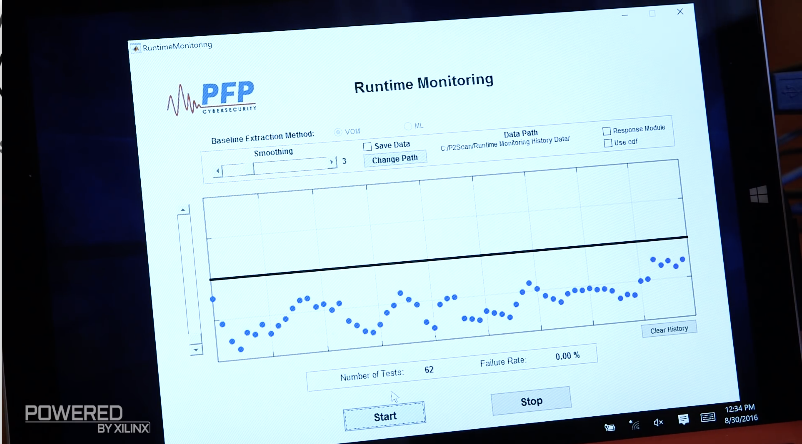
The P2Scan travel kit is a PC-based software containing PFP’s patented power analytics algorithms. The kit provides a user friendly interface with point-and-click simplicity and fully customizable monitoring parameters, sensitivity and metrics. The P2Scan kit includes all of the necessary probes, amplifiers, and analysis software to immediately begin using PFP capability.
PFP’s P1Scan is a firmware can be embedded into ARM- or RISC-V based devices and FPGAs. eMon is the SDK includes P1Scan, reference design, etc.
PFP could be inside the power supply, in between the D.C. power source and the device, or inside the devices. PFP provides a reference design to implement PFP inside a USB Power Adapter and PFP offers breakout boxes or splitters to monitor the signal in between existing power supply and the devices. To be inside the devices, PFP provides reference material which show how to use on-chip ADC or ARM based SoC (system-on-chip) to collect data and connect with the PFP cloud analytics on Amazon Web Services.
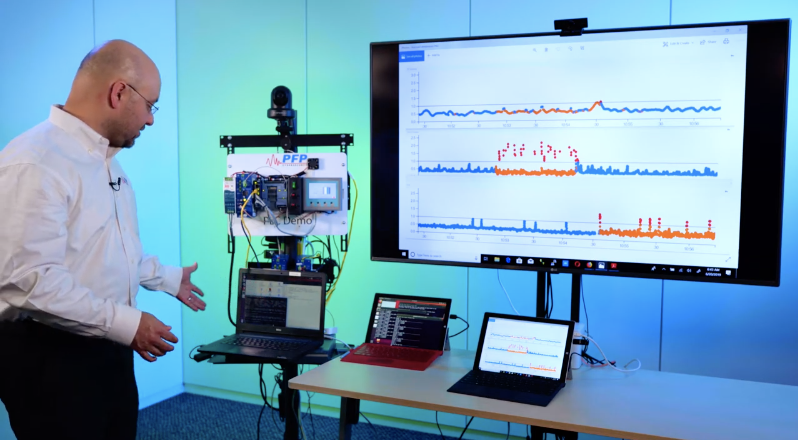
SigLytics can detect and track changes of a device at any point in the product’s lifecycle, from its infancy during manufacturing, through distribution, and even after installation.
Detection with PFP technology is instantaneous, i.e., literally in machine time or milliseconds. With a predefined policy, SigLytics can detect in machine time, interrupt the kill chain, prevent payload be delivered, and stop an attack before damages can occur.
Remediation is a policy-based function. The user sets the policy of what is to happen if a change is detected. For example, reboot, shutdown, re-flash, block all traffic, send alert, reroute traffic, switch control to a clone, etc.
Although TPM and secure boot technologies are good, they are not foolproof. Top data hackers seem to be able to penetrate even the latest cyber security, the AMI firmware supply chain attack allowed tampered firmware became trusted so TPM would not stop it. PFP is a last line of defense, detecting the execution change as soon as the attack first starts.